

Customer service expectations have grown over the last few years. Businesses have had to adapt to meet the needs of their customers. Here are some ways that tech can be implemented to improve the customer service experience.
You can program a chatbot to respond to customers’ immediate needs or questions on your website or app.
With the use of augmented or virtual reality, you can demonstrate how a product will look or work for your customers.
Through certain automation programs, you can ensure that your e-mails appear as if they were tailored for each customer.
Technology experts fear that the next major issue to affect our country will come from the digital world.
During the pandemic, ransomware attacks have increased 500% and don’t seem to be stopping anytime soon.
Ransomware attacks occur when a hacker installs software on a network that prevents the owner from accessing any of their devices or data. They essentially hold the business hostage as they demand a ransom payment.
To combat this, your business needs to put some cyber security practices in place to prevent ransomware attacks. This includes implementing offline backups and keeping your software up-to-date.
The technology your company uses has always been important in attracting experienced and talented employees, but it has become even more important with remote and hybrid work.
Very few employees will want to work remotely for a company that doesn’t provide any of the basic tech needed to perform their role.
A recent study by Barco, Inc. found that 1 in 3 hybrid employees say that one of the top factors in searching for a new job is their frustration while dealing with tech issues.
If you want to retain your top talent, you need to provide your team with the tech needed to perform their daily duties. Check on them to make sure they have everything they need and even the playing field between your remote and in‑office employees.
With the rise in dependability on technology and on the internet, cybercrime is also on the rise. To meet the demand, there is a rising trend of social engineering sites on the dark web, which make malicious hacking a point-and-click exercise. You read correctly, you can now pay for a service to help you commit crime and a new report describes two more sites that were discovered by security researchers.
The first is Ovidiy Stealer, found by Proofpoint, which steals passwords and is marketed on Russian-language website for 7 bucks. It's regularly updated and the sales seem to skyrocket.
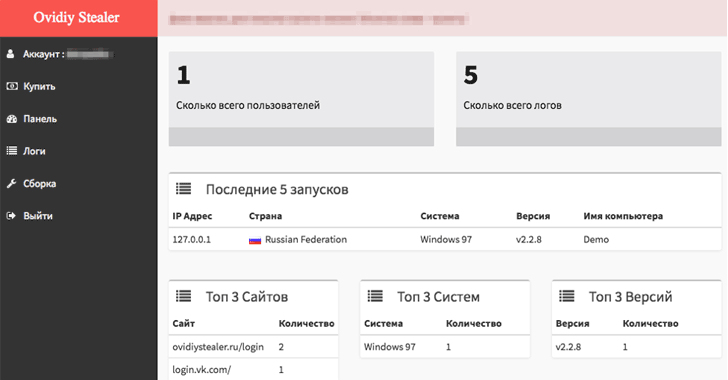
The Ovidiy Stealer malware currently has several versions in the wild, targeting people around the world. It is believed that the malware is currently being spread via email as executable attachments, compressed executable attachments, and links to an executable download. It is also likely spread via file hosting / cracking / keygen sites, where it poses as other software or tools.
Since it has been discovered, the content of this site has been removed. The site itself however, appears to still be online. Below is a list of some of the observed filenames that disguise the malware:
Ovidiy Stealer is written in .NET and most samples are packed with with either .NET Reactor or Confuser. Upon execution the malware will remain in the directory in which it was installed, and where it will carry out tasks. Somewhat surprisingly, there is no persistence mechanism built into this malware, so on reboot it will cease to run, but the file will remain on the victim machine.
Ovidiy Stealer is modular and contains functionality to target a multiple applications -- primarily browsers -- listed below.
The second is Hacksh*t, discovered by the Netskope Threat Research Labs, and is a Phishing-as-a-Service (PhaaS) platform that offers low cost, "automated solution for the beginner scammers."
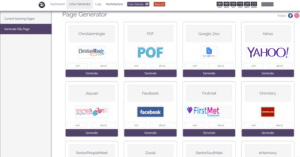
This platform offers free trial accounts to test their hacking tutorials and tricks to make easy money. "The marketplace is a portal that offers services to purchase and sell for carrying out the phishing attacks," Netskope researcher Ashwin Vamshi says.
The Hacksh*t website had a video demonstration appealing users to learning hacking, meeting hackers online and making money. It allows wannabe hackers (subscribers) to generate their unique phishing pages for several services, including Yahoo, Facebook, and Google's Gmail. "The attacker then generates a phished page from the page/generator link and logs into the email account of the compromised victim, views all the contacts and sends an email embedded with the phished link."
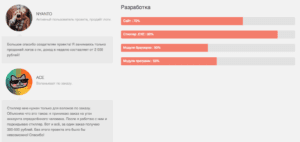
According to Proofpoint, "Like many other markets with many choices, the malware market is competitive and developers must market the strengths and benefits of their products in order to attract buyers. To help drive sales, the development team includes statistics on the progress of certain modules, and other plans for future releases of the malware. In addition, the site includes “testimonials" from satisfied customers, presumably to demonstrate to other would-be criminals that they can be profitable when using Ovidiy Stealer."
Below is a screen capture of the reviews and development progress of Odiviy Stealer. The user ACE’s comments translate to English as: “I only need the stealer for burglary on order. I explain what it is: I accept an order for the hijacking of a certain person's account. After I work with him and install the stealer. That's all, for one order I get 300-500 rubles. Without this project it would be impossible! Thank you!”
It is inevitable that more and more software engineering services will surface. With the internet connecting people worldwide, it certainly comes with its challenges. This is a huge risk for businesses, because they are usually the targets of malware and phishing attacks.
This is why it is important to implement corporate policies and security services to protect company data. Backup and disaster recovery is also a huge component and a requirement in many instances to become operational after an infection.
Of course proactive measures are the first line of defense. Therefore, it is critical for companies to hire knowledgeable IT providers and staff to ensure their data is protected. QWERTY Concepts includes essential security services, such as anti-virus, anti-malware, inbound and outbound email security, backup & disaster recovery, and network security with web content filtering as part of its monthly managed services offering. Schedule a free technology assessment today!
A massive attack, triggered by a version of the GoldenEye or Petya ransomware is currently claiming victims around the world. Unlike other families of ransomware, #GoldenEye does not encrypt individual files, but rather the entire hard disk drive. It then reboots it to prevent the user from accessing that information. When the encryption process is complete, #GoldenEye forcefully crashes the computer and asks for $300 as ransom.
What is unique about #GoldenEye is that unlike other ransomware, this variant has two layers of encryption: once that encrypts files on the computer and another one that encrypts NTFS filesystems. This approach prevents victim computers from being booted up into Windows.
Additionally, after the encryption process is complete, the ransomware has a specialized routine that forcefully crashes the computer to trigger a reboot that renders the computer unusable until the $300 ransom is paid.
According to BitDefender Labs, some infections with GoldenEye/Petya have been triggered by a compromised update of the MeDOC accounting software. It was first intercepted by their customers in Ukraine, therefore confirming the MeDOC update as the infection vector. This makes Ukraine "patient zero" from where the infection spread across networks to headquarters and/or satellite offices.
"Our initial investigation reveals that it spreads automatically from one computer to another using multiple vulnerabilities in the operating system, including the EternalBlue exploit that grabbed the headlines during the #WannaCry attack.", stated BitDefender.
BitDefender Labs also noted that "Several critical infrastructure institutions in Ukraine have already been taken offline." and "We strongly advise all companies who have offices in Ukraine to be on the lookout and to monitor VPN connections to other branches."
It is probably obvious, but everyone is at risk. Even if you are on the latest operating system with the latest Antivirus detection, it is important for all end users to be aware and avoid clicking on files in suspicious emails. It has been confirmed that several companies so far have fallen victim to the #GoldenEye/#Petya ransomware.
Chernobyl’s radiation monitoring system, DLA Piper law firm, pharma company Merck, a number of banks, an airport, the Kiev metro, Danish shipping and energy company Maersk, British advertiser WPP and Russian oil industry company Rosnoft. The attacks were widespread in Ukraine, affecting Ukrenergo, the state power distributor, and several of the country’s banks.
The email address used to get payment confirmation for the ransom has been suspected by Posteo. This means that all payments will be unable to get validated, and therefore will not receive the decryption key. As a result, do not pay the ransom. You'll lose your data anyway, but will also contribute to fund these cyber terrorists for further development of malware.
Our managed services suite includes BitDefender for its endpoint security, who released a statement confirming that Bitdefender blocks the currently known samples of the new #GoldenEye variant and "If you are running a Bitdefender security solution for consumer or business, your computers are not in danger".
Additionally, our managed service plans include email security to block spam and malware externally, before even making it to the network, reducing the risk of infections.

Customer service expectations have grown over the last few years. Businesses have had to adapt to meet the needs of their customers. Here are some ways that tech can be implemented to improve the customer service experience.
You can program a chatbot to respond to customers’ immediate needs or questions on your website or app.
With the use of augmented or virtual reality, you can demonstrate how a product will look or work for your customers.
Through certain automation programs, you can ensure that your e-mails appear as if they were tailored for each customer.
Technology experts fear that the next major issue to affect our country will come from the digital world.
During the pandemic, ransomware attacks have increased 500% and don’t seem to be stopping anytime soon.
Ransomware attacks occur when a hacker installs software on a network that prevents the owner from accessing any of their devices or data. They essentially hold the business hostage as they demand a ransom payment.
To combat this, your business needs to put some cyber security practices in place to prevent ransomware attacks. This includes implementing offline backups and keeping your software up-to-date.
The technology your company uses has always been important in attracting experienced and talented employees, but it has become even more important with remote and hybrid work.
Very few employees will want to work remotely for a company that doesn’t provide any of the basic tech needed to perform their role.
A recent study by Barco, Inc. found that 1 in 3 hybrid employees say that one of the top factors in searching for a new job is their frustration while dealing with tech issues.
If you want to retain your top talent, you need to provide your team with the tech needed to perform their daily duties. Check on them to make sure they have everything they need and even the playing field between your remote and in‑office employees.









