With the rise in dependability on technology and on the internet, cybercrime is also on the rise. To meet the demand, there is a rising trend of social engineering sites on the dark web, which make malicious hacking a point-and-click exercise. You read correctly, you can now pay for a service to help you commit crime and a new report describes two more sites that were discovered by security researchers.
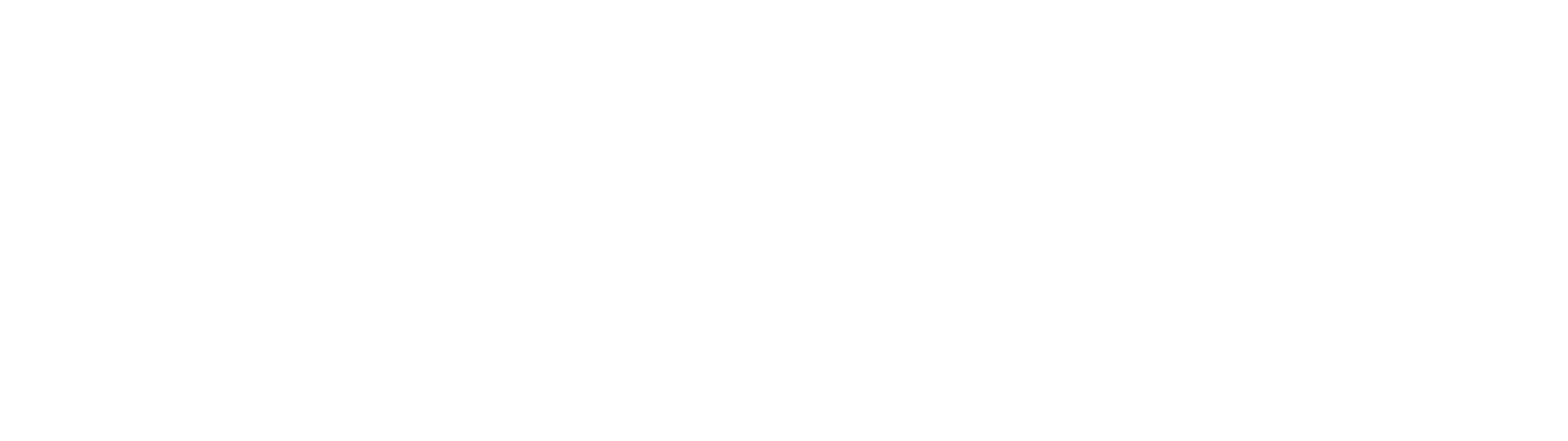
The first is Ovidiy Stealer, found by Proofpoint, which steals passwords and is marketed on Russian-language website for 7 bucks. It's regularly updated and the sales seem to skyrocket.
The Ovidiy Stealer malware currently has several versions in the wild, targeting people around the world. It is believed that the malware is currently being spread via email as executable attachments, compressed executable attachments, and links to an executable download. It is also likely spread via file hosting / cracking / keygen sites, where it poses as other software or tools.
Since it has been discovered, the content of this site has been removed. The site itself however, appears to still be online. Below is a list of some of the observed filenames that disguise the malware:
Ovidiy Stealer is written in .NET and most samples are packed with with either .NET Reactor or Confuser. Upon execution the malware will remain in the directory in which it was installed, and where it will carry out tasks. Somewhat surprisingly, there is no persistence mechanism built into this malware, so on reboot it will cease to run, but the file will remain on the victim machine.
Ovidiy Stealer is modular and contains functionality to target a multiple applications -- primarily browsers -- listed below.
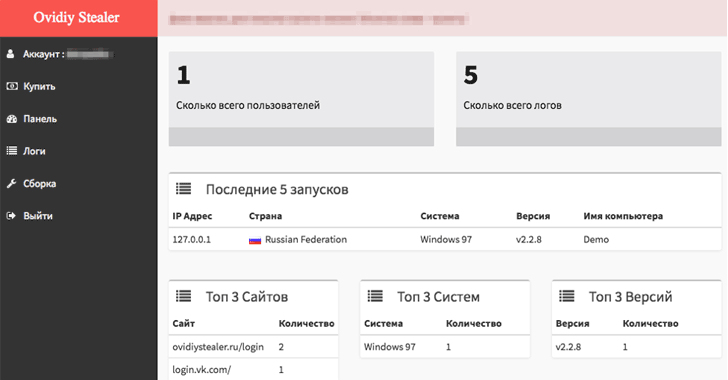
The second is Hacksh*t, discovered by the Netskope Threat Research Labs, and is a Phishing-as-a-Service (PhaaS) platform that offers low cost, "automated solution for the beginner scammers."
This platform offers free trial accounts to test their hacking tutorials and tricks to make easy money. "The marketplace is a portal that offers services to purchase and sell for carrying out the phishing attacks," Netskope researcher Ashwin Vamshi says.
The Hacksh*t website had a video demonstration appealing users to learning hacking, meeting hackers online and making money. It allows wannabe hackers (subscribers) to generate their unique phishing pages for several services, including Yahoo, Facebook, and Google's Gmail. "The attacker then generates a phished page from the page/generator link and logs into the email account of the compromised victim, views all the contacts and sends an email embedded with the phished link."
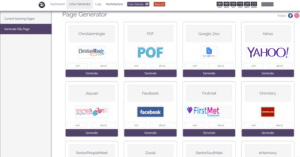
According to Proofpoint, "Like many other markets with many choices, the malware market is competitive and developers must market the strengths and benefits of their products in order to attract buyers. To help drive sales, the development team includes statistics on the progress of certain modules, and other plans for future releases of the malware. In addition, the site includes “testimonials" from satisfied customers, presumably to demonstrate to other would-be criminals that they can be profitable when using Ovidiy Stealer."
Below is a screen capture of the reviews and development progress of Odiviy Stealer. The user ACE’s comments translate to English as: “I only need the stealer for burglary on order. I explain what it is: I accept an order for the hijacking of a certain person's account. After I work with him and install the stealer. That's all, for one order I get 300-500 rubles. Without this project it would be impossible! Thank you!”
It is inevitable that more and more software engineering services will surface. With the internet connecting people worldwide, it certainly comes with its challenges. This is a huge risk for businesses, because they are usually the targets of malware and phishing attacks.
This is why it is important to implement corporate policies and security services to protect company data. Backup and disaster recovery is also a huge component and a requirement in many instances to become operational after an infection.
Of course proactive measures are the first line of defense. Therefore, it is critical for companies to hire knowledgeable IT providers and staff to ensure their data is protected. QWERTY Concepts includes essential security services, such as anti-virus, anti-malware, inbound and outbound email security, backup & disaster recovery, and network security with web content filtering as part of its monthly managed services offering. Schedule a free technology assessment today!