Law firms in New Jersey face a dual challenge in the years ahead: tightening compliance requirements and the constant pressure to operate more efficiently. From client data privacy and e-discovery to secure remote work and specialized legal software, the technology backbone of a modern practice must be both robust and adaptable. Managed IT support providers tailored to the legal industry can help firms meet these demands while freeing up attorneys and staff to focus on their clients.
Compliance for law firms is not a single checklist. It spans ethical guidelines from the American Bar Association (ABA), health data rules under HIPAA for firms handling medical records, and federal procedural rules such as the Federal Rules of Civil Procedure (FRCP). Each of these areas has technology implications that require proactive management.
IT support providers that specialize in legal practices understand these overlapping obligations. For example, one New Jersey provider with over 22 years of experience assisting law firms specifically highlights its ability to help firms comply with ABA guidelines and HIPAA requirements. Another provider, serving New Jersey attorneys since 1996, addresses FRCP compliance and e-discovery needs as a core part of its services. These providers do not just sell technology; they help law firms stay on the right side of evolving regulations.
The ABA Model Rules require lawyers to take reasonable measures to protect client information. For firms working with healthcare clients, HIPAA adds another layer of data protection mandates. Managed IT services that include 24/7 system monitoring and a responsive helpdesk can help prevent data breaches and ensure that security measures are continuously enforced. Firms should look for a provider that explicitly states its experience with ABA and HIPAA compliance, as that signals an understanding of the specific risks law firms face.
The FRCP governs discovery in federal civil cases, including the production of electronically stored information (ESI). Law firms must be able to preserve, collect, and produce data in a defensible manner. IT support providers that address FRCP compliance often offer data backup, business continuity planning, and disaster recovery services. These capabilities ensure that electronic evidence remains intact and that the firm can respond to discovery requests without costly delays or sanctions.
Legal practices depend on specialized applications for case management, billing, document management, and legal research. A generic IT provider may not have the expertise to troubleshoot or optimize these platforms. New Jersey IT support providers that focus on law firms typically support a common set of legal software, including:
One provider includes SmartAdvocate and Westlaw CaseLogistix in its supported list, while another lists iManage among its offerings. Regardless of which applications your firm relies on, confirm that a potential IT partner supports the specific software your attorneys use daily. The same provider that offers unlimited Helpdesk support for managed services can often resolve legal-application issues faster than a generalist.

Efficiency gains from managed IT go beyond fixing broken computers. When a provider handles system monitoring, helpdesk support, and proactive maintenance, law firm staff spend less time dealing with technology problems and more time on billable work.
Key benefits include:
One New Jersey provider emphasizes its responsive helpdesk and 24/7 monitoring as foundational to its legal-industry service. Another offers unlimited Helpdesk support as part of its managed services plans, allowing firms to budget predictable monthly costs instead of paying by the hour for break-fix assistance.
The shift toward hybrid and remote work continues to reshape legal practices. Attorneys need to access case files, billing systems, and court portals from various locations while maintaining the same level of security as the office network. Managed IT providers that serve law firms typically deploy encrypted virtual private networks (VPNs), multi-factor authentication, and endpoint protection to enable secure remote access. They also train staff on best practices to prevent phishing and unauthorized data sharing.

E-discovery is a specialized area of legal technology that involves identifying, preserving, and producing electronic evidence. Law firms handling litigation or regulatory matters must have systems in place to manage ESI efficiently. IT support providers with experience in the legal sector often help firms set up document management platforms, archiving policies, and litigation hold protocols.
One of the New Jersey providers specifically calls out its work with law firms on FRCP and e-discovery compliance. This includes ensuring that data backups are immutable, that email and document archives are searchable, and that chain-of-custody logs are maintained. Without these capabilities, a firm risks spoliation claims or failing to meet court deadlines.
When evaluating IT support providers for a New Jersey law firm, consider experience, certifications, and the specific compliance areas they address. The table below compares two established providers based on publicly available information from their websites. Verify all details directly with the provider before making a decision.
| Feature | Provider A (ICS) | Provider B (powersolution) |
|---|---|---|
| Years serving law firms | Over 22 years | Since 1996 (over 30 years) |
| Compliance focus | ABA guidelines, HIPAA | FRCP, e-discovery |
| Legal software supported | Needles, Sage TimeSlips, SmartAdvocate, LexisNexis PCLaw, Time Matters, Westlaw CaseLogistix, Amicus Attorney | Needles, Sage TimeSlips, iManage, LexisNexis PCLaw, Time Matters, Westlaw, Amicus Attorney |
| Key services | 24/7 monitoring, responsive helpdesk, network support | Unlimited Helpdesk, data backup, disaster recovery, business continuity |
| Certifications / ratings | Microsoft Certified Silver Partner, SOC II certified, A+ BBB rating | Industry awards (details on provider site) |
Both providers also address client confidentiality and data security, which are paramount for any law firm. Another New Jersey IT support company, Monmouth Cyber, also offers services for legal firms with a focus on client confidentiality and compliance.
When comparing providers, ask how they handle software updates for legal applications, what their typical helpdesk response time is, and whether they offer a free assessment or consultation. For law firms expecting growth, scalability should also be a consideration: can the provider add new users and locations quickly without disrupting operations?

Managed IT providers that specialize in law firms usually support platforms such as Needles, Sage TimeSlips, LexisNexis PCLaw, Time Matters, Amicus Attorney, SmartAdvocate, Westlaw CaseLogistix, and iManage. Always check with the provider to confirm that your specific applications are included in their scope of support.
ABA ethical rules require lawyers to protect client information from unauthorized access. Managed IT providers help enforce security measures such as encryption, multi-factor authentication, and secure backups. They also monitor networks 24/7 and provide staff training to reduce the risk of data breaches that could violate confidentiality obligations.
E-discovery is the process of identifying, preserving, and producing electronically stored information (ESI) in litigation or investigations. Law firms must manage ESI defensively to comply with the Federal Rules of Civil Procedure. IT support providers can implement document management systems, litigation hold tools, and immutable backups to help firms meet discovery deadlines.
Secure remote work requires encrypted VPN connections, multi-factor authentication, and endpoint antivirus software. Managed IT providers also train staff on recognizing phishing attempts and secure password practices. These measures allow attorneys to access case files and billing systems from home or travel locations without exposing client data to additional risk.
Certifications like Microsoft Silver or Gold Partner status, SOC II reporting, and a high Better Business Bureau rating indicate a provider’s commitment to quality and security. For law firms, the provider should also demonstrate specific experience with legal software and compliance frameworks such as ABA, HIPAA, and FRCP.
Law firms in New Jersey that invest in specialized IT support are better positioned to meet 2026 compliance demands while improving daily efficiency. By partnering with a provider that understands legal software, data privacy, and regulatory obligations, firms can reduce risk and focus on what they do best: serving their clients.
In a recent cybersecurity incident, hackers exploited a previously patched vulnerability in Roundcube, an open-source webmail software. This stored cross-site scripting (XSS) flaw, identified as CVE-2024-37383, has been used to steal user credentials, raising serious concerns for organizations using the platform. This attack serves as a reminder of the persistent risks associated with vulnerabilities in widely used software and the importance of keeping systems up-to-date.
The vulnerability, which has a CVSS score of 6.1, was discovered earlier this year and was patched in May 2024 with updates to versions 1.5.7 and 1.6.7 of Roundcube. Despite the patch, cybercriminals continue to exploit the flaw by targeting organizations that have not yet applied the update. The stored XSS vulnerability leverages SVG animate attributes to execute arbitrary JavaScript code within the victim’s web browser, leading to potential data breaches.
The cybersecurity firm Positive Technologies discovered this exploit when they intercepted an email sent to a government organization in one of the Commonwealth of Independent States (CIS). The intercepted email appeared harmless, containing only a blank document attachment. However, upon investigation, the email was found to contain tags designed to decode and execute JavaScript code upon opening.
The attack begins when a user receives an email containing hidden malicious code within its body. When the email is opened in Roundcube, the embedded JavaScript code is executed, initiating a series of malicious actions:
This sophisticated chain of events enables hackers to gain access to the user’s login credentials and potentially other sensitive information stored within the compromised mail server.
Roundcube, while not the most widely used email client, is popular among government agencies and other organizations handling sensitive information. This makes it an attractive target for cybercriminals seeking high-value data. The potential consequences of such an exploit can be severe, particularly if sensitive governmental or proprietary information is accessed and exfiltrated.
The slow adoption of software updates further exacerbates the threat posed by such vulnerabilities. Despite the patches being available since May 2024, organizations that fail to update their systems remain at risk. This incident highlights the critical importance of maintaining up-to-date software to avoid falling victim to known exploits.
The exact perpetrators behind the Roundcube XSS exploit remain unidentified. However, past vulnerabilities in the platform have been targeted by advanced persistent threat (APT) groups such as APT28, Winter Vivern, and TAG-70. These groups are known for their sophisticated espionage activities and their focus on government and high-value organizational data.
While there is no direct attribution in this case, the sophisticated nature of the attack chain suggests that skilled and possibly state-sponsored actors could be involved.
This incident underscores the importance of timely software updates and the need for heightened vigilance in cybersecurity practices. Organizations using Roundcube or similar open-source software should take proactive measures to protect their systems. This includes regularly applying patches, conducting vulnerability assessments, and educating employees about phishing attacks and other risks.
Moreover, implementing multi-layered security protocols can help organizations mitigate the risk of similar attacks in the future. Multi-factor authentication (MFA), intrusion detection systems, and real-time monitoring can provide an additional layer of defense against such exploits.
The Roundcube XSS vulnerability incident is a cautionary tale for organizations relying on open-source webmail software. While patches were released earlier this year, the failure to promptly update systems has left many organizations exposed to sophisticated cyberattacks. By exploiting unpatched systems, hackers have demonstrated their ability to bypass traditional security measures and gain access to sensitive information.
To mitigate the risks posed by such vulnerabilities, organizations must prioritize cybersecurity best practices, such as regular updates, employee training, and comprehensive monitoring. Staying informed about the latest threats and taking proactive measures to secure digital assets is key to minimizing the impact of cyberattacks.
For those interested in staying up-to-date with cybersecurity news and expert insights, subscribing to newsletters and attending industry webinars can be valuable resources for keeping your organization protected.
As the rest of us, scammers too, love travel season. They know your eyes are peeled for a cheap plane ticket and have devised convincing ways to scam you.
Tricked consumers have spent months of their lives dealing with the consequences of these scams and lost thousands of dollars in the process.
In a recent plague of travel scams, criminals are pretending to be “travel agents” selling plane tickets.
There are a handful of tactics travel scammers use to steal your information.
These are all major red flags to watch out for. Before clicking or booking anything, pay attention to these travel tips to avoid getting scammed out of thousands of dollars of your hard-earned vacation savings.
Stay informed, pay attention and implement these practical tips for your next adventure. Safe travels! Be sure to check out another post on social media scams.
The dark web is a part of the internet that requires special software to access. Often used by individuals who are looking to conceal their identities and activities, it has become the ideal environment for cybercriminals seeking to carry out illicit activities. They can move anonymously in this part of the internet often engaging in criminal activities such as the sale of stolen data, hacking tools, illegal drugs, counterfeit documents, and even illicit services.
While the dark web may seem distant and irrelevant to your everyday business operations, it poses serious risks that can have far-reaching consequences. Here's why you need to be aware of it:
To protect your business from the risks associated with the Dark Web, we recommend the following actions:
We are committed to staying ahead of emerging cybersecurity threats and providing you with the necessary tools and expertise to safeguard your business.
If you are not sure where to start protecting your business against data breaches, why don’t start by knowing the current status of your business’ data?
We can help you protect your business by running an initial dark web scan to see if any of your data is on the for sale on the dark web. After the scan is completed, we will go over the results with you, helping you identify and take action about the data already leaked and also helping you establish a plan to prevent future breaches. Click here to get started with your free dark web scan.
Cyber threats are always on the rise, and businesses are constantly looking for ways to protect themselves. One of the most effective ways to train your team is through gamification.
Gamification is the process of using game design elements and principles in non-game contexts to engage users and solve problems. It is a powerful tool that can help organizations improve employee training and development.
Gamification can be used to create immersive and interactive learning experiences that are more engaging and effective than traditional training methods.
It makes learning more fun and interactive by incorporating game elements such as points, badges, levels, and leaderboards. This helps employees stay engaged and motivated to learn!
We include this approach in our own cybersecurity training program for your team.
It includes phishing simulations and scenarios that replicate real-world cybersecurity threats. This allows employees to experience and learn how to deal with cyber-attacks in a safe and controlled environment.
This can provide immediate feedback to employees, allowing them to learn from their mistakes and improve their skills. This can help identify areas where employees need further training or support.
It can also reinforce learning by incorporating repetition and feedback. This can help employees retain information and apply it in real-life situations.
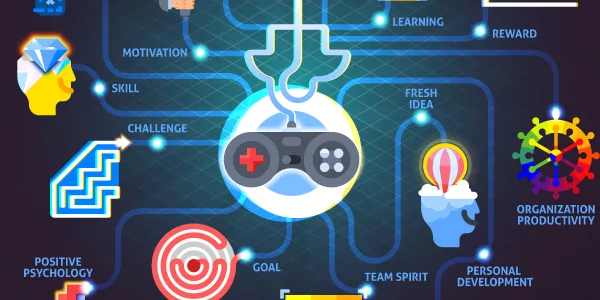
And the final reason we include gamification in our cybersecurity training program, it’s fun.
Gamification can create a sense of competition and motivation to learn among employees. This can lead to improved learning outcomes and a stronger cybersecurity culture within the organization.
Gamification sure is an effective tool for training employees and improving cybersecurity.
It is just one component of our cybersecurity training solution. By making learning more engaging, interactive, and effective, it can lead to a better-trained workforce and a more secure organization.
As cyber threats continue to evolve, organizations must invest in employee training and development to stay ahead of the curve.
We can help your business to achieve a well-trained workforce in cybersecurity, just give us a call at 732-926-0112 or leave us a message here, and one of our cyber security experts will get in touch with you.
As a small or medium-sized business (SMB) owner, you may not have the same level of resources as large corporations. However, that doesn't mean you should overlook the importance of protecting your business from cyber threats.
Identifying the most critical aspects of your business that need protection and focusing your resources on those areas is a star.
There’s also another component that can protect the business as a whole: your team.
The "MVP" or Most Valuable Player mindset puts your employees at the forefront of defense.
We can help you to make your entire team a roster of MVPs.
We’ll perform a cyber security risk assessment to identify gaps on your current defenses or any potential risks.
This cyber security risk assessment will review the following in your business:
We will identify which of these assets are critical to your business's success and could cause the most damage if they were compromised.
Next, we’ll implement measures to protect those critical assets.
These cybersecurity measures include:
We will also implement our ongoing cybersecurity training program.
This will help your employees recognize and avoid potential threats like phishing emails or malware.
Then we’ll create a plan in place for responding to a cyber-attack.
This will include clear protocols for reporting and responding to security incidents, and make sure all employees are aware of the steps they should take in the event of an attack.
We’ll reinforce your business cyber-defenses by regularly review and update your cybersecurity measures as new threats emerge.
By taking a proactive approach to cybersecurity and focusing your resources on protecting your most valuable assets, you can help reduce the risk of a damaging cyber-attack on your SMB.
You will also contribute to reducing the costs of insurance and cyber insurance for your business.
If you don’t currently have any proactive cybersecurity plan ongoing or if you want to strengthen the one you currently have, we can help!
Give us a call to 732-926-0112 or leave us a message here, and one of our cyber security experts will get in touch with you.
If you’ve turned on the news sometime during the past few years, you must have heard of more than one instance where a business closed due to a cyber attack.
You may think your business is small enough and hackers won’t target you, but this couldn’t be further from the truth. Every business is at risk of experiencing a cyber attack and should be well-prepared to defend against these threats.
With the right type of attack, a cybercriminal gains valuable information about your business, customers and employees, which can be used to damage your reputation and hurt you financially.
If you’re a business owner or leader and you want to ensure your business is well-protected, check out the most common cyber attacks that are affecting companies today. From there, you can implement cybersecurity plans and tactics to ensure your business is protected from cybercriminals.
Phishing is a type of social engineering where an attacker sends a fraudulent message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious software on the victim’s infrastructure.
Phishing scams wreak havoc on your business and personal life.
You may have seen an e-mail from someone claiming to be Amazon or your credit card company asking for specific sensitive information. Often, the e-mail address does not line up with who the person is claiming to be.
When a phishing scam targets your business, they request valuable information from your employees, such as passwords or customer data. If your employees fall for the scam, they could give a cybercriminal access to your network and systems.
This will also allow the cybercriminal to steal private employee and customer information, leaving your employees vulnerable to identity theft.
Phishing scams can be averted by using common sense and providing cyber security training to your employees.
Most companies will not request private information over e-mail. That being said, if an employee receives a suspicious e-mail, they should do their due diligence to ensure the e-mail is genuine before responding in any way.
These are some steps that anyone in your company can take to detect a phishing email:
If your business falls victim to a cyber-attack, it could have lasting consequences for you, your employees, and your clients.
Malware is software installed on a computer without the user’s consent that performs malicious actions, such as stealing passwords or money.
There are many types of malware, including spyware, viruses, ransomware and adware.
You can accidentally download malware onto your computer by clicking on sketchy links within e-mails or websites.
Your computer may be infected with malware right now and you do not even know it. These are a few hints that can help you identify whether you have been infected with malware or not:
Prevention is key in stopping malware from affecting your business.
Hiring and utilizing a managed services provider is the best way to protect your business, as they will continually monitor your network and proactively secure your network.
With malware, it’s always better to play it safe than sorry. If a cybercriminal is able to use ransomware on your network, your business could be stuck at a standstill until you pay the ransom. Even if you can pay the ransom, your reputation will still take a hit, and your business could be greatly affected.
Be careful where you click on your phone, too, since malware attacks on cellphones have become more common over the past few years.
How do your employees access your network or computer systems? They use a password to log in to their computer, access their e-mail and much more.
What would happen if someone with bad intentions gained access to one of your employee’s passwords? Depending on the individual’s access, they could obtain sensitive information about your business, customers, and employees.
Your team should be using long, complex passwords for their accounts, and each password for every account should be different. Encourage your employees to use password managers that will allow them to create the most complex passwords possible and keep track of them more easily. You can also provide a corporate password manager for all your business’ email accounts. Some MSPs include essential tools in their managed service plans. Be sure to utilize these tools.
Incorporate multifactor authentication (MFA) to ensure nobody can steal a password and gain access immediately.
All of these password hygiene best practices have to be included in your business’ Password security training.
If your business falls victim to a cyber-attack, it could have lasting consequences for you, your employees, and your clients. Now that you know the most common types of cyber-attacks, you can start implementing plans to ensure you and your business stay protected.
If you don’t have any cybersecurity training plan in place or if your current training program feels incomplete, we can help you set up a comprehensive annual cyber security training program for everyone in your company. Additionally, we offer a free dark web scan. Simply enter your business email address and receive a free report, instantly.
In yet another phishing email hoax, the New York State DMV is now cautioning consumers against an email "phishing" campaign. This phishing attempt sends a notice to email users stating they must pay a ticket within 48 hours or their license will be revoked. While the notice is made to appear as if it comes from DMV, it is a hoax.
Though the recent press release is from the New York State Department of Motor Vehicles, campaigns for other states may be soon be phishing for personal information as well. The NY DMV advises that the "Email falsely claims to be from New York State DMV". The DMV also advises to "not click on links".
The phishing email hoax targets New York drivers, stating they have 48 hours to pay a fine or have their driver's license revoked. The NY DMV alerted motorists that the scam is just bait to entice them to click on a “payment” link. Once clicked, it will in turn infect their workstation with malware. The DMV does not know how many people have been affected, but Owen McShane, director of investigations at New York State DMV, said calls came in from New York City, Albany and Syracuse.
Olenick also went into more detail stating "The malware being dropped came in two categories. The first simply placed a tracking tool on the victim's computer to see what websites were visited; and the second, more nefarious, attempted to acquire a variety of personally identifiable information, such as names, Social Security numbers, date of birth and credit card information."
There are several red flags that show the email is a scam. The supplied links lead to sites without an ny.gov URL, tied to the fact that the state would never make such a request. The hoax email lists a reference number and then reads something like this:
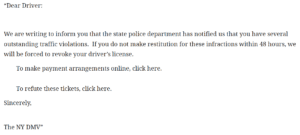
“The Department of Motor Vehicles does not send emails urging motorists to pay traffic tickets within 48 hours or lose your license,” said Terri Egan, DMV deputy executive commissioner, in a statement.
We suggest you send your employees, co-workers, friends, and family an email about this scam, feel free to copy/paste/edit:
"Here is a reminder that you need to be alert for fake emails that look like they come from your local police or State Dept of Motor Vehicles (DMV) claiming you have a traffic violation. At the moment, there is a local scam in New York that falsely states you have outstanding violations you need to either pay for or refute, and if you don't your license will be revoked. This scam may spread to the rest of America soon. Remember that citations are never emailed with links in them, or sent out with an email attachment, and report scams like this to your local police department."
Obviously, an end-user who was trained to spot these red flags like this would have thought before they clicked. Additionally, email security solutions will likely trap these types of emails before they reach the mailbox.
We strongly suggest you get a quote for email security services for your organization - you'd be surprised how affordable they are. Contact us for a quote, today!
Reference: https://dmv.ny.gov/press-release/press-release-06-01-2017
DocuSign, a major provider of electronic signature technology based in San Francisco, admitted that a series of recent phishing malware attacks targeting its customers and users was the result of a data breach at one of its computer systems. The company stresses that the data stolen was limited to customer and user email addresses. The incident is especially dangerous, because it allows attackers to target users who may already be expecting emails from DocuSign. This form of attack is known as phishing attempts.
DocuSign warned on May 9 that it was tracking a malicious email campaign where the subject line reads, “Completed: docusign.com – Wire Transfer Instructions for recipient-name Document Ready for Signature.” The email contained a link to a downloadable Microsoft Word document. The attachment contains malware, and tricks users into activating Word's macro feature, which will download and install malware on the user's workstation.
The company initially dismissed that the messages were associated with DocuSign and that they were sent from a malicious third party. However, in an update on Monday, DocuSign confirmed that this malicious third party was able to send the messages to DocuSign's customers and users because it had broken in and stolen their list of customers and users.
“As part of our ongoing investigation, today we confirmed that a malicious third party had gained temporary access to a separate, non-core system that allows us to communicate service-related announcements to users via email,” DocuSign wrote in an alert posted to its site. “A complete forensic analysis has confirmed that only email addresses were accessed; no names, physical addresses, passwords, social security numbers, credit card data or other information was accessed. No content or any customer documents sent through DocuSign’s eSignature system was accessed; and DocuSign’s core eSignature service, envelopes and customer documents and data remain secure.”
They are advising customers to filter or delete any emails with specific subject lines. These email subjects look something like:
Completed: [domain name] – "Wire transfer for recipient-name Document Ready for Signature"
Completed [domain name/email address] – "Accounting Invoice [Number] Document Ready for Signature"
Subject: “Legal acknowledgement for [recipient username] Document is Ready for Signature”
Since the recent newsworthy security breaches, it is becoming critical to educate employees on identifying and handling potential threats. Bringing awareness is not enough, however. Due to the human factor, many email solutions, whether they are cloud-based or on-premise, integrate with outside email security services. These that filter and quarantine potential threats before they arrive to the email server and even network. QWERTY Concepts, provides email security services for their cloud platform, office 365, and to on-premise email servers. Click here to receive a free consultation and quote.
The company is asking people to forward suspicious emails related to DocuSign to [email protected].
Law firms in New Jersey face a dual challenge in the years ahead: tightening compliance requirements and the constant pressure to operate more efficiently. From client data privacy and e-discovery to secure remote work and specialized legal software, the technology backbone of a modern practice must be both robust and adaptable. Managed IT support providers tailored to the legal industry can help firms meet these demands while freeing up attorneys and staff to focus on their clients.
Compliance for law firms is not a single checklist. It spans ethical guidelines from the American Bar Association (ABA), health data rules under HIPAA for firms handling medical records, and federal procedural rules such as the Federal Rules of Civil Procedure (FRCP). Each of these areas has technology implications that require proactive management.
IT support providers that specialize in legal practices understand these overlapping obligations. For example, one New Jersey provider with over 22 years of experience assisting law firms specifically highlights its ability to help firms comply with ABA guidelines and HIPAA requirements. Another provider, serving New Jersey attorneys since 1996, addresses FRCP compliance and e-discovery needs as a core part of its services. These providers do not just sell technology; they help law firms stay on the right side of evolving regulations.
The ABA Model Rules require lawyers to take reasonable measures to protect client information. For firms working with healthcare clients, HIPAA adds another layer of data protection mandates. Managed IT services that include 24/7 system monitoring and a responsive helpdesk can help prevent data breaches and ensure that security measures are continuously enforced. Firms should look for a provider that explicitly states its experience with ABA and HIPAA compliance, as that signals an understanding of the specific risks law firms face.
The FRCP governs discovery in federal civil cases, including the production of electronically stored information (ESI). Law firms must be able to preserve, collect, and produce data in a defensible manner. IT support providers that address FRCP compliance often offer data backup, business continuity planning, and disaster recovery services. These capabilities ensure that electronic evidence remains intact and that the firm can respond to discovery requests without costly delays or sanctions.
Legal practices depend on specialized applications for case management, billing, document management, and legal research. A generic IT provider may not have the expertise to troubleshoot or optimize these platforms. New Jersey IT support providers that focus on law firms typically support a common set of legal software, including:
One provider includes SmartAdvocate and Westlaw CaseLogistix in its supported list, while another lists iManage among its offerings. Regardless of which applications your firm relies on, confirm that a potential IT partner supports the specific software your attorneys use daily. The same provider that offers unlimited Helpdesk support for managed services can often resolve legal-application issues faster than a generalist.

Efficiency gains from managed IT go beyond fixing broken computers. When a provider handles system monitoring, helpdesk support, and proactive maintenance, law firm staff spend less time dealing with technology problems and more time on billable work.
Key benefits include:
One New Jersey provider emphasizes its responsive helpdesk and 24/7 monitoring as foundational to its legal-industry service. Another offers unlimited Helpdesk support as part of its managed services plans, allowing firms to budget predictable monthly costs instead of paying by the hour for break-fix assistance.
The shift toward hybrid and remote work continues to reshape legal practices. Attorneys need to access case files, billing systems, and court portals from various locations while maintaining the same level of security as the office network. Managed IT providers that serve law firms typically deploy encrypted virtual private networks (VPNs), multi-factor authentication, and endpoint protection to enable secure remote access. They also train staff on best practices to prevent phishing and unauthorized data sharing.

E-discovery is a specialized area of legal technology that involves identifying, preserving, and producing electronic evidence. Law firms handling litigation or regulatory matters must have systems in place to manage ESI efficiently. IT support providers with experience in the legal sector often help firms set up document management platforms, archiving policies, and litigation hold protocols.
One of the New Jersey providers specifically calls out its work with law firms on FRCP and e-discovery compliance. This includes ensuring that data backups are immutable, that email and document archives are searchable, and that chain-of-custody logs are maintained. Without these capabilities, a firm risks spoliation claims or failing to meet court deadlines.
When evaluating IT support providers for a New Jersey law firm, consider experience, certifications, and the specific compliance areas they address. The table below compares two established providers based on publicly available information from their websites. Verify all details directly with the provider before making a decision.
| Feature | Provider A (ICS) | Provider B (powersolution) |
|---|---|---|
| Years serving law firms | Over 22 years | Since 1996 (over 30 years) |
| Compliance focus | ABA guidelines, HIPAA | FRCP, e-discovery |
| Legal software supported | Needles, Sage TimeSlips, SmartAdvocate, LexisNexis PCLaw, Time Matters, Westlaw CaseLogistix, Amicus Attorney | Needles, Sage TimeSlips, iManage, LexisNexis PCLaw, Time Matters, Westlaw, Amicus Attorney |
| Key services | 24/7 monitoring, responsive helpdesk, network support | Unlimited Helpdesk, data backup, disaster recovery, business continuity |
| Certifications / ratings | Microsoft Certified Silver Partner, SOC II certified, A+ BBB rating | Industry awards (details on provider site) |
Both providers also address client confidentiality and data security, which are paramount for any law firm. Another New Jersey IT support company, Monmouth Cyber, also offers services for legal firms with a focus on client confidentiality and compliance.
When comparing providers, ask how they handle software updates for legal applications, what their typical helpdesk response time is, and whether they offer a free assessment or consultation. For law firms expecting growth, scalability should also be a consideration: can the provider add new users and locations quickly without disrupting operations?

Managed IT providers that specialize in law firms usually support platforms such as Needles, Sage TimeSlips, LexisNexis PCLaw, Time Matters, Amicus Attorney, SmartAdvocate, Westlaw CaseLogistix, and iManage. Always check with the provider to confirm that your specific applications are included in their scope of support.
ABA ethical rules require lawyers to protect client information from unauthorized access. Managed IT providers help enforce security measures such as encryption, multi-factor authentication, and secure backups. They also monitor networks 24/7 and provide staff training to reduce the risk of data breaches that could violate confidentiality obligations.
E-discovery is the process of identifying, preserving, and producing electronically stored information (ESI) in litigation or investigations. Law firms must manage ESI defensively to comply with the Federal Rules of Civil Procedure. IT support providers can implement document management systems, litigation hold tools, and immutable backups to help firms meet discovery deadlines.
Secure remote work requires encrypted VPN connections, multi-factor authentication, and endpoint antivirus software. Managed IT providers also train staff on recognizing phishing attempts and secure password practices. These measures allow attorneys to access case files and billing systems from home or travel locations without exposing client data to additional risk.
Certifications like Microsoft Silver or Gold Partner status, SOC II reporting, and a high Better Business Bureau rating indicate a provider’s commitment to quality and security. For law firms, the provider should also demonstrate specific experience with legal software and compliance frameworks such as ABA, HIPAA, and FRCP.
Law firms in New Jersey that invest in specialized IT support are better positioned to meet 2026 compliance demands while improving daily efficiency. By partnering with a provider that understands legal software, data privacy, and regulatory obligations, firms can reduce risk and focus on what they do best: serving their clients.









